A Ukrainian man indicted in 2012 for conspiring with a prolific hacking group to steal tens of hundreds of thousands of {dollars} from U.S. companies was arrested in Italy and is now in custody in the USA, KrebsOnSecurity has discovered.
Sources near the investigation say Yuriy Igorevich Rybtsov, a 41-year-old from the Russia-controlled metropolis of Donetsk, Ukraine, was beforehand referenced in U.S. federal charging paperwork solely by his on-line deal with “MrICQ.” Based on a 13-year-old indictment (PDF) filed by prosecutors in Nebraska, MrICQ was a developer for a cybercrime group often known as “Jabber Zeus.”
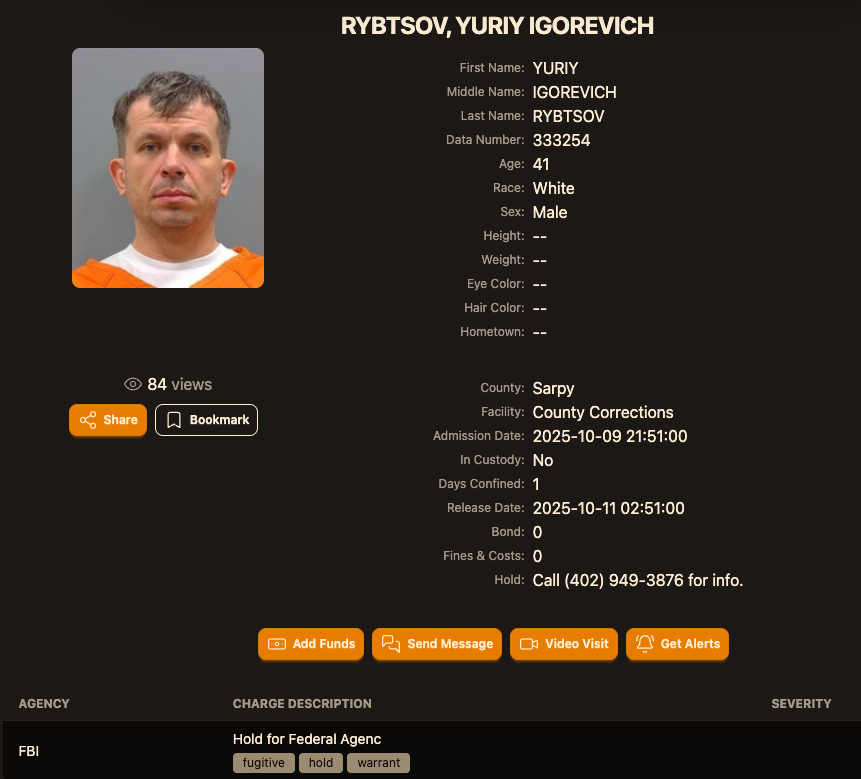
Picture: lockedup dot wtf.
The Jabber Zeus title is derived from the malware they used — a customized model of the ZeuS banking trojan — that stole banking login credentials and would ship the group a Jabber prompt message every time a brand new sufferer entered a one-time passcode at a monetary establishment web site. The gang focused principally small to mid-sized companies, they usually have been an early pioneer of so-called “man-in-the-browser” assaults, malware that may silently intercept any knowledge that victims submit in a web-based type.
As soon as inside a sufferer firm’s accounts, the Jabber Zeus crew would modify the agency’s payroll so as to add dozens of “cash mules,” folks recruited by way of elaborate work-at-home schemes to deal with financial institution transfers. The mules in flip would ahead any stolen payroll deposits — minus their commissions — by way of wire transfers to different mules in Ukraine and the UK.
The 2012 indictment focusing on the Jabber Zeus crew named MrICQ as “John Doe #3,” and stated this individual dealt with incoming notifications of newly compromised victims. The Division of Justice (DOJ) stated MrICQ additionally helped the group launder the proceeds of their heists by way of digital foreign money change providers.
Two sources conversant in the Jabber Zeus investigation stated Rybtsov was arrested in Italy, though the precise date and circumstances of his arrest stay unclear. A abstract of current selections (PDF) revealed by the Italian Supreme Courtroom states that in April 2025, Rybtsov misplaced a remaining enchantment to keep away from extradition to the USA.
Based on the mugshot web site lockedup[.]wtf, Rybtsov arrived in Nebraska on October 9, and was being held underneath an arrest warrant from the U.S. Federal Bureau of Investigation (FBI).
The info breach monitoring service Constella Intelligence discovered breached information from the enterprise profiling web site bvdinfo[.]com exhibiting {that a} 41-year-old Yuriy Igorevich Rybtsov labored in a constructing at 59 Barnaulska St. in Donetsk. Additional looking out on this handle in Constella finds the identical house constructing was shared by a enterprise registered to Vyacheslav “Tank” Penchukov, the chief of the Jabber Zeus crew in Ukraine.

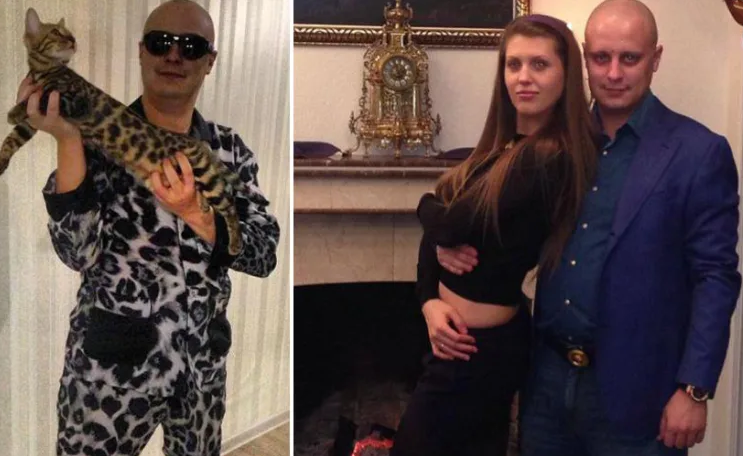
Vyacheslav “Tank” Penchukov, seen right here performing as “DJ Slava Wealthy” in Ukraine, in an undated picture from social media.
Penchukov was arrested in 2022 whereas touring to satisfy his spouse in Switzerland. Final 12 months, a federal courtroom in Nebraska sentenced Penchukov to 18 years in jail and ordered him to pay greater than $73 million in restitution.
Lawrence Baldwin is founding father of myNetWatchman, a risk intelligence firm based mostly in Georgia that started monitoring and disrupting the Jabber Zeus gang in 2009. myNetWatchman had secretly gained entry to the Jabber chat server utilized by the Ukrainian hackers, permitting Baldwin to snoop on the day by day conversations between MrICQ and different Jabber Zeus members.
Baldwin shared these real-time chat information with a number of state and federal regulation enforcement companies, and with this reporter. Between 2010 and 2013, I spent a number of hours every day alerting small companies throughout the nation that their payroll accounts have been about to be drained by these cybercriminals.
These notifications, and Baldwin’s tireless efforts, saved numerous would-be victims a substantial amount of cash. Typically, nevertheless, we have been already too late. However, the pilfered Jabber Zeus group chats offered the premise for dozens of tales revealed right here about small companies combating their banks in courtroom over six- and seven-figure monetary losses.
Baldwin stated the Jabber Zeus crew was far forward of its friends in a number of respects. For starters, their intercepted chats confirmed they labored to create a extremely personalized botnet immediately with the writer of the unique Zeus Trojan — Evgeniy Mikhailovich Bogachev, a Russian man who has lengthy been on the FBI’s “Most Wished” listing. The feds have a standing $3 million reward for info resulting in Bogachev’s arrest.
Evgeniy M. Bogachev, in undated images.
The core innovation of Jabber Zeus was an alert that MrICQ would obtain every time a brand new sufferer entered a one-time password code right into a phishing web page mimicking their monetary establishment. The gang’s inner title for this element was “Leprechaun,” (the video under from myNetWatchman exhibits it in motion). Jabber Zeus would really re-write the HTML code as displayed within the sufferer’s browser, permitting them to intercept any passcodes despatched by the sufferer’s financial institution for multi-factor authentication.
“These guys had compromised such numerous victims that they have been getting buried in a tsunami of stolen banking credentials,” Baldwin advised KrebsOnSecurity. “However the entire level of Leprechaun was to isolate the highest-value credentials — the business financial institution accounts with two-factor authentication turned on. They knew these have been far juicier targets as a result of they clearly had much more cash to guard.”
Baldwin stated the Jabber Zeus trojan additionally included a customized “backconnect” element that allowed the hackers to relay their checking account takeovers by way of the sufferer’s personal contaminated PC.
“The Jabber Zeus crew have been actually connecting to the sufferer’s checking account from the sufferer’s IP handle, or from the distant management perform and by totally emulating the system,” he stated. “That trojan was like a scorching knife by way of butter of what everybody thought was state-of-the-art safe on-line banking on the time.”
Though the Jabber Zeus crew was in direct contact with the Zeus writer, the chats intercepted by myNetWatchman present Bogachev incessantly ignored the group’s pleas for assist. The federal government says the true chief of the Jabber Zeus crew was Maksim Yakubets, a 38-year Ukrainian man with Russian citizenship who glided by the hacker deal with “Aqua.”
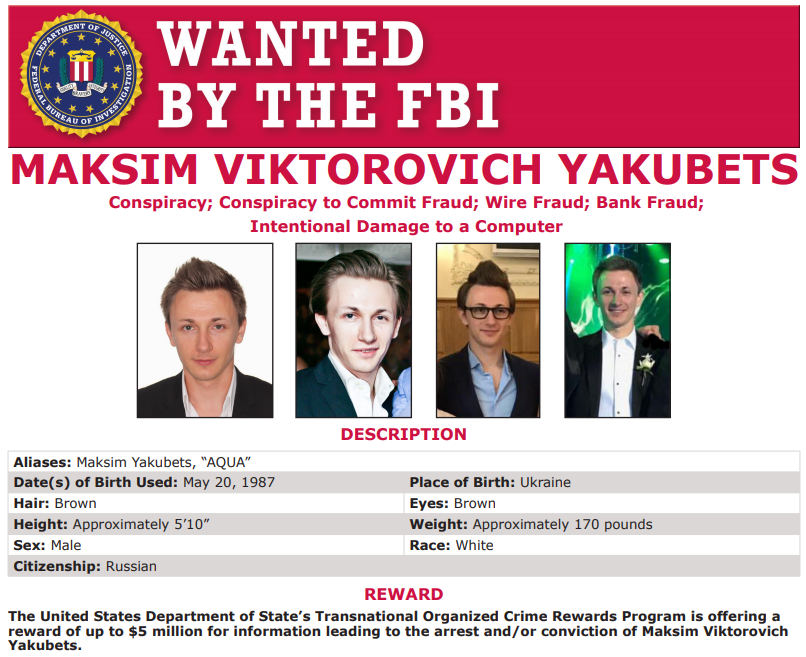
Alleged Evil Corp chief Maksim “Aqua” Yakubets. Picture: FBI
The Jabber chats intercepted by Baldwin present that Aqua interacted nearly day by day with MrICQ, Tank and different members of the hacking workforce, typically facilitating the group’s cash mule and cashout actions remotely from Russia.
The federal government says Yakubets/Aqua would later emerge because the chief of an elite cybercrime ring of no less than 17 hackers that referred to themselves internally as “Evil Corp.” Members of Evil Corp developed and used the Dridex (a.okay.a. Bugat) trojan, which helped them siphon greater than $100 million from a whole bunch of sufferer corporations in the USA and Europe.
This 2019 story concerning the authorities’s $5 million bounty for info resulting in Yakubets’s arrest consists of excerpts of conversations between Aqua, Tank, Bogachev and different Jabber Zeus crew members discussing tales I’d written about their victims. Each Baldwin and I have been interviewed at size for a brand new weekly six-part podcast by the BBC that delves deep into the historical past of Evil Corp. Episode One focuses on the evolution of Zeus, whereas the second episode facilities on an investigation into the group by former FBI agent Jim Craig.

Picture:
