Encryption of each information at relaxation and in transit is a non-negotiable characteristic for many organizations. Moreover, organizations working in extremely regulated and security-sensitive environments—equivalent to these within the monetary sector—usually require full management over the cryptographic keys used for his or her workloads.
Amazon Managed Service for Apache Flink makes it simple to course of real-time information streams with strong security measures, together with encryption by default to assist defend your information in transit and at relaxation. The service removes the complexity of managing the important thing lifecycle and controlling entry to the cryptographic materials.
If it’s worthwhile to retain full management over your key lifecycle and entry, Managed Service for Apache Flink now helps using buyer managed keys (CMKs) saved in AWS Key Administration Service (AWS KMS) for encrypting software information.
This characteristic helps you handle your individual encryption keys and key insurance policies, so you may meet strict compliance necessities and keep full management over delicate information. With CMK integration, you may reap the benefits of the scalability and ease of use that Managed Service for Apache Flink provides, whereas assembly your group’s safety and compliance insurance policies.
On this submit, we discover how the CMK performance works with Managed Service for Apache Flink functions, the use instances it unlocks, and key concerns for implementation.
Information encryption in Managed Service for Apache Flink
In Managed Service for Apache Flink, there are a number of points the place information must be encrypted:
- Information at relaxation straight managed by the service – Sturdy software storage (checkpoints and snapshots) and working software state storage (disk volumes utilized by RocksDB state backend) are mechanically encrypted
- Information in transit inner to the Flink cluster – Mechanically encrypted utilizing TLS/HTTPS
- Information in transit to and at relaxation in exterior methods that your Flink software accesses – For instance, an Amazon Managed Streaming for Apache Kafka (Amazon MSK) subject by means of the Kafka connector or calling an endpoint by means of a customized AsyncIO); encryption will depend on the exterior service, person settings, and code
For information at relaxation managed by the service, checkpoints, snapshots, and working software state storage are encrypted by default utilizing AWS owned keys. In case your safety necessities require you to straight management the encryption keys, you should utilize the CMK held in AWS KMS.
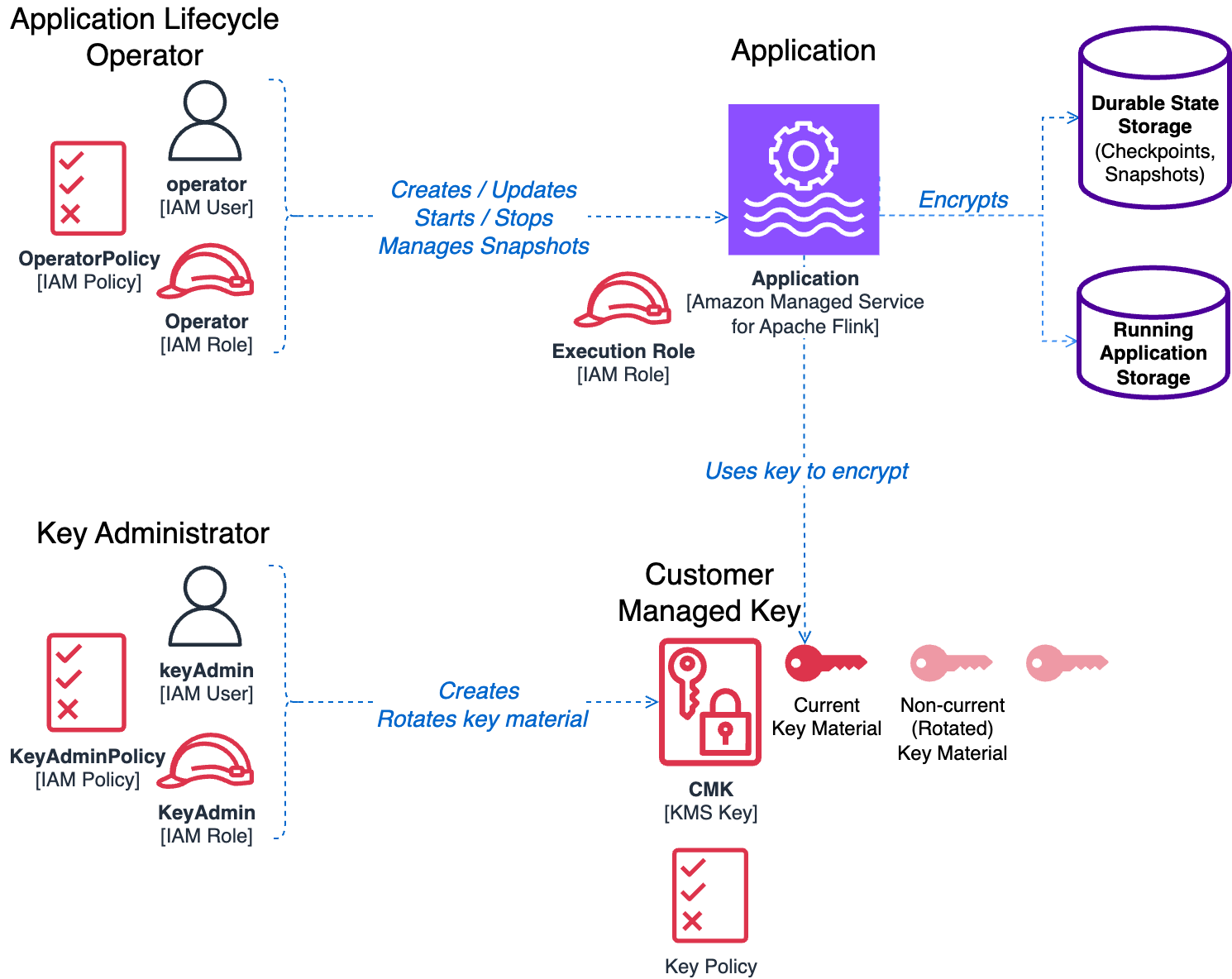
Key parts and roles
To grasp how CMKs work in Managed Service for Apache Flink, we first have to introduce the parts and roles concerned in managing and working an software utilizing CMK encryption:
- Buyer managed key (CMK):
- Resides in AWS KMS inside the identical AWS account as your software
- Has an connected key coverage that defines entry permissions and utilization rights to different parts and roles
- Encrypts each sturdy software storage (checkpoints and snapshots) and working software state storage
- Managed Service for Apache Flink software:
- The applying whose storage you wish to encrypt utilizing the CMK
- Has an connected AWS Id and Entry Administration (IAM) execution position that grants permissions to entry exterior providers
- The execution position doesn’t have to supply any particular permissions to make use of the CMK for encryption operations
- Key administrator:
- Manages the CMK lifecycle (creation, rotation, coverage updates, and so forth)
- Might be an IAM person or IAM position, and utilized by a human operator or by automation
- Requires administrative entry to the CMK
- Permissions are outlined by the connected IAM insurance policies and the important thing coverage
- Software operator:
- Manages the applying lifecycle (begin/cease, configuration updates, snapshot administration, and so forth)
- Might be an IAM Consumer or IAM position, and utilized by a human operator or by automation
- Requires permissions to handle the Flink software and use the CMK for encryption operations
- Permissions are outlined by the connected IAM insurance policies and the important thing coverage
The next diagram illustrates the answer structure.
Enabling CMK following the precept of least privilege
When deploying functions in manufacturing environments or dealing with delicate information, it’s best to comply with the precept of least privilege. CMK help in Managed Service for Apache Flink has been designed with this precept in thoughts, so every element receives solely the minimal permissions essential to operate.
For detailed details about the permissions required by the applying operator and key coverage configurations, check with Key administration in Amazon Managed Service for Apache Flink. Though these insurance policies would possibly seem advanced at first look, this complexity is intentional and crucial. For extra particulars concerning the necessities for implementing essentially the most restrictive key administration doable whereas sustaining performance, check with Least-privilege permissions.
For this submit, we spotlight some essential factors about CMK permissions:
- Software execution position – Requires no further permissions to make use of a CMK. You don’t want to vary the permissions of an current software; the service handles CMK operations transparently throughout runtime.
- Software operator permissions – The operator is the person or position who controls the applying lifecycle. For the permissions required to function an software that makes use of CMK encryption, check with Key administration in Amazon Managed Service for Apache Flink. Along with these permissions, an operator usually has permissions on actions with the
kinesisanalyticsprefix. It’s a finest follow to limit these permissions to a particular software defining theUseful resource. The operator should even have theiam:PassRolepermission to go the service execution position to the applying.
To simplify managing the permissions of the operator, we suggest creating two separate IAM insurance policies, to be connected to the operator’s position or person:
- A base operator coverage defining the fundamental permissions to function the applying lifecycle with no CMK
- A further CMK operator coverage that provides permissions to function the applying with a CMK
The next IAM coverage instance illustrates the permissions that must be included within the base operator coverage:
Discuss with Software lifecycle operator (API caller) permissions for the permissions to be included with the extra CMK operator coverage.
Separating these two insurance policies has an extra good thing about simplifying the method of organising an software for the CMK, as a result of dependencies we illustrate within the following part.
Dependencies between the important thing coverage and CMK operator coverage
In case you fastidiously observe the operator’s permissions and the important thing coverage defined in Create a KMS key coverage, you’ll discover some interdependencies, illustrated by the next diagram.
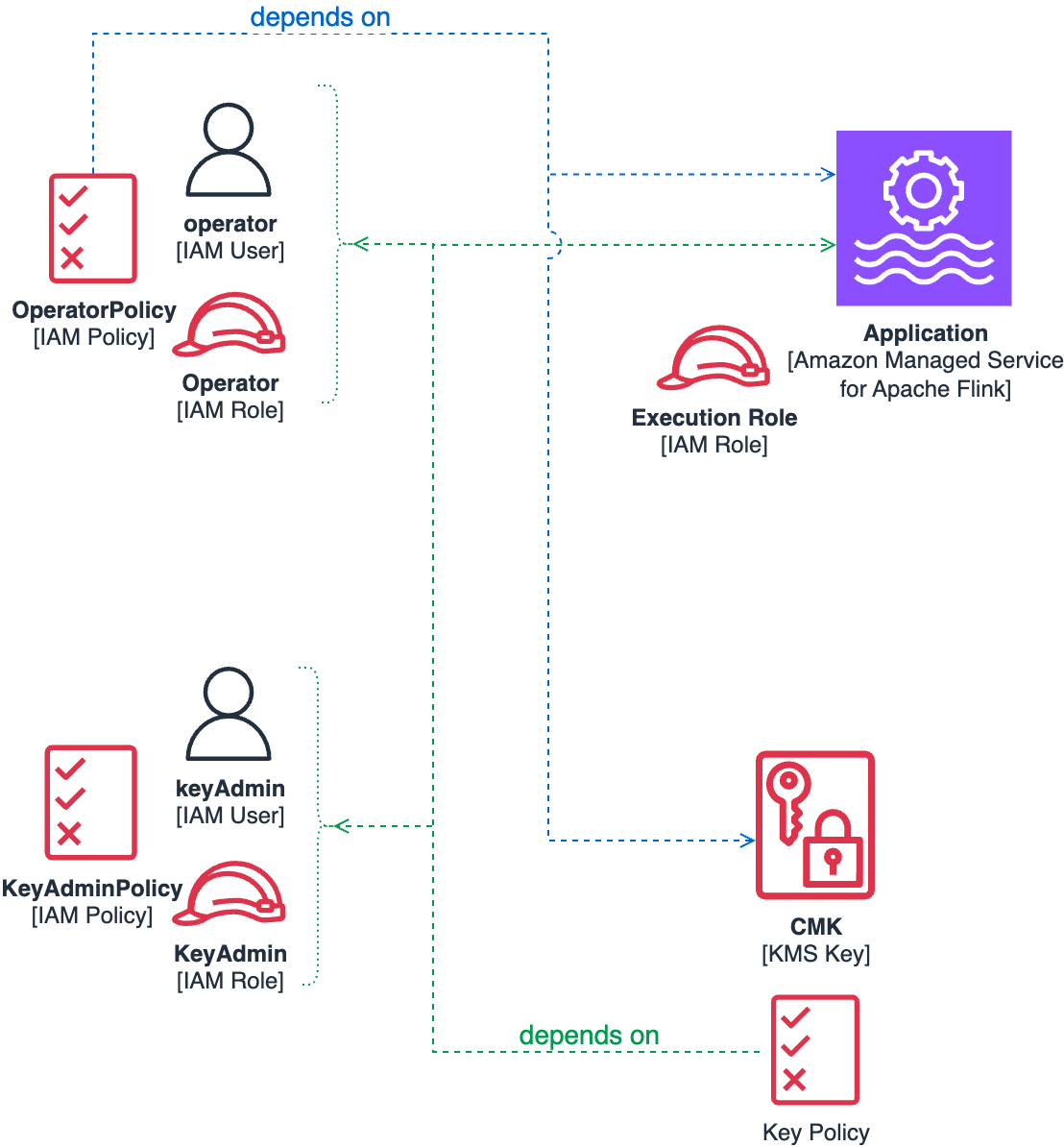
Particularly, we spotlight the next:
- CMK key coverage dependencies – The CMK coverage requires references to each the applying Amazon Useful resource Title (ARN) and the important thing administrator or operator IAM roles or customers. This coverage should be outlined at key creation time by the important thing administrator.
- IAM coverage dependencies – The operator’s IAM coverage should reference each the applying ARN and the CMK key itself. The operator position is answerable for numerous duties, together with configuring the applying to make use of the CMK.
To correctly comply with the precept of least privilege, every element requires the others to exist earlier than it may be accurately configured. This necessitates a fastidiously orchestrated deployment sequence.
Within the following part, we reveal the exact order required to resolve these dependencies whereas sustaining safety finest practices.
Sequence of operations to create a brand new software with a CMK
When deploying a brand new software that makes use of CMK encryption, we suggest following this sequenced method to resolve dependency conflicts whereas sustaining safety finest practices:
- Create the operator IAM position or person with a base coverage that features software lifecycle permissions. Don’t embody CMK permissions at this stage, as a result of the important thing doesn’t exist but.
- The operator creates the applying utilizing the default AWS owned key. Preserve the applying in a stopped state to forestall information creation—there must be no information at relaxation to encrypt throughout this section.
- Create the important thing administrator IAM position or person, if not already accessible, with permissions to create and handle KMS keys. Discuss with Utilizing IAM insurance policies with AWS KMS for detailed permission necessities.
- The important thing administrator creates the CMK in AWS KMS. At this level, you’ve got the required parts for the important thing coverage: software ARN, operator IAM position or person ARN, and key administrator IAM position or person ARN.
- Create and connect to the operator an extra IAM coverage that features the CMK-specific permissions. See Software lifecycle operator (API caller) permissions for the entire operator coverage definition.
- The operator can now modify the applying configuration utilizing the
UpdateApplicationmotion, to allow CMK encryption, as illustrated within the following part. - The applying is now able to run with all information at relaxation encrypted utilizing your CMK.
Allow the CMK with UpdateApplication
You may configure a Managed Service for Apache Flink software to make use of a CMK utilizing the AWS Administration Console, the AWS API, AWS Command Line Interface (AWS CLI), or infrastructure as code (IaC) instruments just like the AWS Cloud Improvement Package (AWS CDK) or AWS CloudFormation templates.
When organising CMK encryption in a manufacturing surroundings, you’ll in all probability use an automation instrument somewhat than the console. These instruments finally use the AWS API below the hood, and the UpdateApplication motion of the kinesisanalyticsv2 API particularly. On this submit, we analyze the additions to the API that you should utilize to regulate the encryption configuration.
A further top-level block ApplicationEncryptionConfigurationUpdate has been added to the UpdateApplication request payload. With this block, you may allow and disable the CMK.
It’s essential to add the next block to the UpdateApplication request:
The KeyIdUpdate worth may be the important thing ARN, key ID, key alias identify, or key alias ARN.
Disable the CMK
Equally, the next requests disable the CMK, switching again to the default AWS owned key:
Allow the CMK with CreateApplication
Theoretically, you may allow the CMK straight if you first create the applying utilizing the CreateApplication motion.
A top-level block ApplicationEncryptionConfiguration has been added to the CreateApplication request payload, with a syntax much like UpdateApplication.
Nevertheless, as a result of interdependencies described within the earlier part, you’ll most frequently create an software with the default AWS owned key and later use UpdateApplication to allow the CMK.
In case you omit ApplicationEncryptionConfiguration if you create the applying, the default habits is utilizing the AWS owned key, for backward compatibility.
Pattern CloudFormation templates to create IAM roles and the KMS key
The method you employ to create the roles and key and configure the applying to make use of the CMK will fluctuate, relying on the automation you employ and your approval and safety processes. Any automation instance we will present will doubtless not suit your processes or tooling.
Nevertheless, the next GitHub repository supplies some instance CloudFormation templates to generate a number of the IAM insurance policies and the KMS key with the right key coverage:
- IAM coverage for the important thing administrator – Permits managing the important thing
- Base IAM coverage for the operator – Permits managing the conventional software lifecycle operations with out the CMK
- CMK IAM coverage for the operator – Offers further permissions required to handle the applying lifecycle when the CMK is enabled
- KMS key coverage – Permits the applying to encrypt and decrypt the applying state and the operator to handle the applying operations
CMK operations
We’ve described the method of making a brand new Managed Service for Apache Flink software with CMK. Let’s now look at different widespread operations you may carry out.
Adjustments to the encryption key change into efficient when the applying is restarted. In case you replace the configuration of a working software, this causes the applying to restart and the brand new key for use instantly. Conversely, should you change the important thing of a READY (not working) software, the brand new key will not be really used till the applying is restarted.
Allow a CMK on an current software
You probably have an software working with an AWS owned key, the method is much like what we described for creating new functions. On this case, you have already got a working software state and older snapshots which might be encrypted utilizing the AWS owned key.
Additionally, when you’ve got a working software, you in all probability have already got an operator position with an IAM coverage that you should utilize to regulate the operator lifecycle.
The sequence of steps to allow a CMK on an current and working software is as follows:
- In case you don’t have already got one, create a key administrator IAM position or person with permissions to create and handle keys in AWS KMS. See Utilizing IAM insurance policies with AWS KMS for extra particulars concerning the permissions required to handle keys.
- The important thing administrator creates the CMK. The important thing coverage references the applying ARN, the operator’s ARN, and the important thing administrator’s position or person ARN.
- Create an extra IAM coverage that permits using the CMK and connect this coverage to the operator. Alternatively, modify the operator’s current IAM coverage by including these permissions.
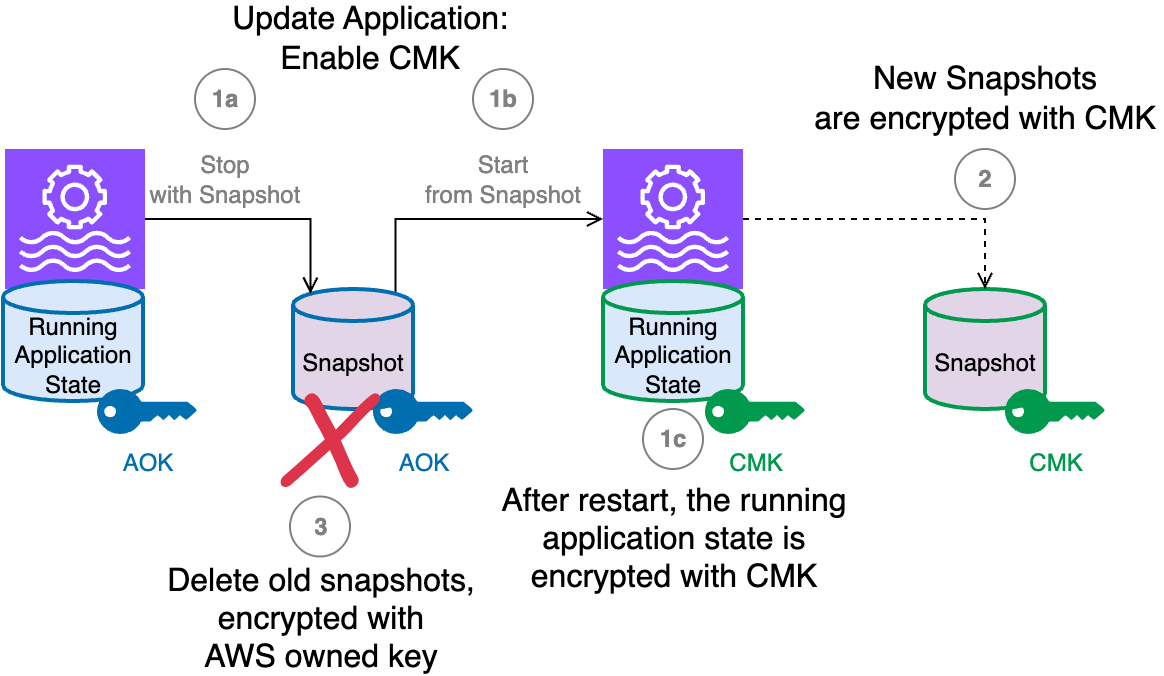
- Lastly, the operator can replace the applying and allow the CMK.The next diagram illustrates the method that happens if you execute an
UpdateApplicationmotion on the working software to allow a CMK.
The workflow consists of the next steps:
- If you replace the applying to arrange the CMK, the next occurs:
- The applying working state, in the meanwhile it’s encrypted with the AWS owned key, is saved in a snapshot whereas the applying is stopped. This snapshot is encrypted with the default AWS owned key. The working software state storage is unstable and destroyed when the applying is stopped.
- The applying is redeployed, restoring the snapshot into the working software state.
- The working software state storage is now encrypted with the CMK.
- New snapshots created from this level on are encrypted utilizing the CMK.
- You’ll in all probability wish to delete all of the outdated snapshots, together with the one created mechanically by the
UpdateApplicationthat enabled the CMK, as a result of they’re all encrypted utilizing the AWS owned key.
Rotate the encryption key
As with all cryptographic key, it’s a finest follow to rotate the important thing periodically for enhanced safety. Managed Service for Apache Flink doesn’t help AWS KMS automated key rotation, so you’ve got two main choices for rotating your CMK.
Choice 1: Create a brand new CMK and replace the applying
The primary method includes creating a wholly new KMS key after which updating your software configuration to make use of the brand new key. This technique supplies a clear separation between the outdated and new encryption keys, making it simpler to trace which information was encrypted with which key model.
Let’s assume you’ve got a working software utilizing CMK#1 (the present key) and wish to rotate to CMK#2 (the brand new key) for enhanced safety:
- Conditions and preparation – Earlier than initiating the important thing rotation course of, you need to replace the operator’s IAM coverage to incorporate permissions for each CMK#1 and CMK#2. This dual-key entry helps uninterrupted operation throughout the transition interval. After the applying configuration has been efficiently up to date and verified, you may safely take away all permissions to CMK#1.
- Software replace course of – The
UpdateApplicationoperation used to configure CMK#2 mechanically triggers an software restart. This restart mechanism makes positive each the applying’s working state and any newly created snapshots are encrypted utilizing the brand new CMK#2, offering quick safety advantages from the up to date encryption key. - Vital safety concerns – Present snapshots, together with the automated snapshot created throughout the CMK replace course of, stay encrypted with the unique CMK#1. For full safety hygiene and to attenuate your cryptographic footprint, contemplate deleting these older snapshots after verifying that your software is functioning accurately with the brand new encryption key.
This method supplies a clear separation between outdated and new encrypted information whereas sustaining software availability all through the important thing rotation course of.
Choice 2: Rotate the important thing materials of the prevailing CMK
The second choice is to rotate the cryptographic materials inside your current KMS key. For a CMK used for Managed Service for Apache Flink, we suggest utilizing on-demand key materials rotation.
The good thing about this method is simplicity: no change is required to the applying configuration nor to the operator’s IAM permissions.
Vital safety concerns
The brand new encryption secret’s utilized by the Managed Service for Apache Flink software solely after the following software restart. To make the brand new key materials efficient, instantly after the rotation, it’s worthwhile to cease and begin utilizing snapshots to protect the applying state or execute an UpdateApplication, which additionally forces a stop-and-restart. After the restart, it’s best to contemplate deleting the outdated snapshots, together with the one taken mechanically within the final stop-and-restart.
Swap again to the AWS owned key
At any time, you may determine to change again to utilizing an AWS owned key. The applying state remains to be encrypted, however utilizing the AWS owned key as a substitute of your CMK.
If you’re utilizing the UpdateApplication API or AWS CLI command to change again to CMK, you need to explicitly go ApplicationEncryptionConfigurationUpdate, setting the important thing kind to AWS_OWNED_KEY as proven within the following snippet:
If you execute UpdateApplication to change off the CMK, the operator should nonetheless have permissions on the CMK. After the applying is efficiently working utilizing the AWS owned key, you may safely take away any CMK-related permissions from the operator’s IAM coverage.
Check the CMK in improvement environments
In a manufacturing surroundings—or an surroundings containing delicate information—it’s best to comply with the precept of least privilege and apply the restrictive permissions described to date.
Nevertheless, if you wish to experiment with CMKs in a improvement setting, equivalent to utilizing the console, strictly following the manufacturing course of would possibly change into cumbersome. In these environments, the roles of key administrator and operator are sometimes crammed by the identical particular person.
For testing functions in improvement environments, you would possibly wish to use a permissive key coverage like the next, so you may freely experiment with CMK encryption:
This coverage mustn’t ever be utilized in an surroundings containing delicate information, and particularly not in manufacturing.
Frequent caveats and pitfalls
As mentioned earlier, this characteristic is designed to maximise safety and promote finest practices such because the precept of least privilege. Nevertheless, this focus can introduce some nook instances you have to be conscious of.
The CMK should be enabled for the service to encrypt and decrypt snapshots and working state
With AWS KMS, you may disable one key at any time. In case you disable the CMK whereas the applying is working, it’d trigger unpredictable failures. For instance, an software will be unable to revive a snapshot if the CMK used to encrypt that snapshot has been disabled. For instance, should you try to roll again an UpdateApplication that modified the CMK, and the earlier key has since been disabled, you may not have the ability to restore from an outdated snapshot. Equally, you may not have the ability to restart the applying from an older snapshot if the corresponding CMK is disabled.
In case you encounter these situations, the answer is to reenable the required key and retry the operation.
The operator requires permissions to all keys concerned
To carry out an motion on the applying (equivalent to Begin, Cease, UpdateApplication, or CreateApplicationSnapshot), the operator will need to have permissions for all CMKs concerned in that operation. AWS owned keys don’t require specific permission.
Some operations implicitly contain two CMKs—for instance, when switching from one CMK to a different, or when switching from a CMK to an AWS owned key by disabling the CMK. In these instances, the operator will need to have permissions for each keys for the operation to succeed.
The identical rule applies when rolling again an UpdateApplication motion that concerned a number of CMKs.
A brand new encryption key takes impact solely after restart
A brand new encryption secret’s solely used after the applying is restarted. That is essential if you rotate the important thing materials for a CMK. Rotating the important thing materials in AWS KMS doesn’t require updating the Managed Flink software’s configuration. Nevertheless, you need to restart the applying as a separate step after rotating the important thing. In case you don’t restart the applying, it can proceed to make use of the outdated encryption key for its working state and snapshots till the following restart.
For that reason, it is strongly recommended to not allow automated key rotation for the CMK. When automated rotation is enabled, AWS KMS would possibly rotate the important thing materials at any time, however your software won’t begin utilizing the brand new key till it’s subsequent restarted.
CMKs are solely supported with Flink runtime 1.20 or later
CMKs are solely supported when you find yourself utilizing the Flink runtime 1.20 or later. In case your software is at the moment utilizing an older runtime, it’s best to improve to Flink 1.20 first. Managed Service for Apache Flink makes it simple to improve your current software utilizing the in-place model improve.
Conclusion
Managed Service for Apache Flink supplies strong safety by enabling encryption by default, defending each the working state and persistently saved state of your functions. For organizations that require full management over their encryption keys (usually on account of regulatory or inner coverage wants), the flexibility to make use of a CMK built-in with AWS KMS provides a brand new stage of assurance.
Through the use of CMKs, you may tailor encryption controls to your particular compliance necessities. Nevertheless, this flexibility comes with the necessity for cautious planning: the CMK characteristic is deliberately designed to implement the precept of least privilege and powerful position separation, which might introduce complexity round permissions and operational processes.
On this submit, we reviewed the important thing steps for enabling CMKs on current functions, creating new functions with a CMK, and managing key rotation. Every of those processes provides you better management over your information safety but additionally requires consideration to entry administration and operational finest practices.
To get began with CMKs and for extra complete steering, check with Key administration in Amazon Managed Service for Apache Flink.